
|
Lujo Bauer
Professor,
Electrical & Computer Engineering + Computer Science (Software and Societal Systems Department)
Please consider submitting a paper or attending:
|

|
Lujo Bauer
Professor,
Electrical & Computer Engineering + Computer Science (Software and Societal Systems Department)
Please consider submitting a paper or attending:
|
Fall 2026: Special Topics in Security: ML for Cybersecurity (17-739)
Spring 2026: Special Topics in Security: ML for Cybersecurity (18-739c)
Fall 2024: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818)
Fall 2023: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818)
Spring 2023: Introduction to Computer Security (15-330 / 18-330)
Fall 2022: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818)
Previous...
Spring 2022: Introduction to Computer Security (15-330 / 18-330)
Fall 2021: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818)
Spring 2021: Introduction to Computer Security (15-330 / 18-330)
Fall 2020: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818)
Spring 2020: Introduction to Computer Security (15-330 / 18-330)
Fall 2019: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818) (previously 8-533 / 8-733)
Spring 2019: Secure Software Systems (18-335 / 18-732)
Fall 2018: Privacy Policy, Law, and Technology (17-333 / 17-733 / 19-608 / 95-818) (previously 8-533 / 8-733)
Spring 2018: Secure Software Systems (18-732)
Fall 2017: Privacy Policy, Law, and Technology (8-533 / 8-733 / 19-608 / 95-818)
Spring 2017: Secure Software Systems (18-732)
Fall 2016: Privacy Policy, Law, and Technology (8-533 / 8-733 / 19-608 / 95-818)
Spring 2016: Usable Privacy and Security (05-436 / 05-836 / 08-534 / 08-734 / 19-534 / 19-734)
Spring 2016: Secure Software Systems (18-732)
Fall 2015: Introduction to Computer Security (18-730)
Fall 2015: Information Security & Privacy (15-421 / 08-731 / 08-761 / 45-885 / 45-985)
Spring 2015: Secure Software Systems (18-732)
Fall 2014: Information Security and Privacy (08-731 / 15-421 / 08-761 / 45-885 / 45-985)
Spring 2014: Secure Software Systems (18-732)
Spring 2013: Secure Software Systems (18-732)
Fall 2011: Intro to Computer & Network Security & Applied Cryptography (18-487)
Fall 2010: Secure Software Systems (18-732)
Fall 2009: Introduction to Security and Policy (18-630 / 19-631 / 95-830)
Fall 2008: Secure Software Systems (18-732)
Fall 2007: Introduction to Computer Security (18-730)
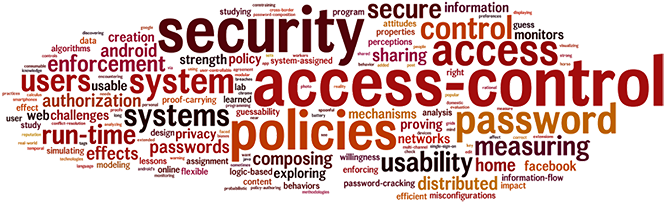
I do research on many aspects of computer security and privacy. I'm particularly interested in usable security and privacy, adversarial machine learning, the security of smarthomes, the risks of online tracking, and user authentication.
Here are some topics that I currently research:
Adversarial ML: Machine learning (ML) algorithms are becoming ubiquitous; they're used in applications from playing chess and predicting the weather to cancer diagnosis and self-driving cars. Our research attempts to discover how robust ML algorithms are in the face of an adversary. Specifically, we study whether an adversary can fool ML classifiers in practical settings without arousing the suspicion of a human. For instance, we showed that it is possible to 3d print a pair of eyeglasses that, when worn by an adversary, can cause a state-of-the-art face-recognition algorithm to identify the adversary as (a specific) someone else. We leverage what we learn of ML algorithms' weaknesses to design ML algorithms that are more resistant to attack.
Training robust ML-based raw-binary malware detectors in hours, not months. Group-based robustness: A general framework for customized robustness in the real world. Adversarial training for raw-binary malware classifiers. Constrained Gradient Descent: a powerful and principled evasion attack against neural networks. Malware makeover: breaking ML-based static analysis by modifying executable bytes. n-ML: Mitigating adversarial examples via ensembles of topologically manipulated classifiers. Optimization-guided binary diversification to mislead neural networks for malware detection. A general framework for adversarial examples with objectives. On the suitability of Lp-norms for creating and preventing adversarial examples. Adversarial Generative Nets: Neural network attacks on state-of-the-art face recognition. Accessorize to a crime: Real and stealthy attacks on state-of-the-art face recognition. Publications
Keane Lucas, Weiran Lin, Lujo Bauer, Michael K. Reiter, and Mahmood Sharif.
In Proceedings of the 31st ACM SIGSAC Conference on Computer and Communications Security, October 2024. © authors DOI: 10.1145/3658644.3690208
[PDF, BibTeX, ]
Weiran Lin, Keane Lucas, Neo Eyal, Lujo Bauer, Michael K. Reiter, and Mahmood Sharif.
In Proceedings of the 31st Network and Distributed System Security Symposium, February 2024. Internet Society. © authors DOI: 10.14722/ndss.2024.24084
[PDF, BibTeX, talk video, ]
Keane Lucas, Samruddhi Pai, Weiran Lin, Lujo Bauer, Michael K. Reiter, and Mahmood Sharif.
In Proceedings of the 32nd USENIX Security Symposium, August 2023. USENIX.
[PDF, BibTeX, talk video and slides, ]
Weiran Lin, Keane Lucas, Lujo Bauer, Michael K. Reiter, and Mahmood Sharif.
In Proceedings of the 39th International Conference on Machine Learning, ICML 2022, July 2022.
[PDF, BibTeX, talk video, talk slides, ]
Keane Lucas, Mahmood Sharif, Lujo Bauer, Michael K. Reiter, and Saurabh Shintre.
In Proceedings of the ACM Asia Conference on Computer and Communications Security, June 2021. © authors DOI: 10.1145/3433210.3453086
[PDF, BibTeX, slides, talk video, code, ]
Mahmood Sharif, Lujo Bauer, and Michael K. Reiter.
arXiv preprint 1912.09059, December 2019.
[PDF, BibTeX, project page, ]
Mahmood Sharif, Keane Lucas, Lujo Bauer, Michael K. Reiter, and Saurabh Shintre.
arXiv preprint 1912.09064, December 2019.
[PDF, BibTeX, project page, ]
Mahmood Sharif, Sruti Bhagavatula, Lujo Bauer, and Michael K. Reiter.
ACM Transactions on Privacy and Security, 22 (3). June 2019. (Revised version of arXiv preprint 1801.00349.) © authors DOI: 10.1145/3317611
[PDF, BibTeX, project page, ]
Mahmood Sharif, Lujo Bauer, and Michael K. Reiter.
In Proceedings of The Bright and Dark Sides of Computer Vision: Challenges and Opportunities for Privacy and Security (in conjunction with the 2018 IEEE Conference on Computer Vision and Pattern Recognition), June 2018. © IEEE
[PDF, BibTeX, project page, ]
Mahmood Sharif, Sruti Bhagavatula, Lujo Bauer, and Michael K. Reiter.
arXiv preprint 1801.00349, December 2017.
[PDF, BibTeX, project page, ]
Mahmood Sharif, Sruti Bhagavatula, Lujo Bauer, and Michael K. Reiter.
In Proceedings of the 23rd ACM SIGSAC Conference on Computer and Communications Security, October 2016. DOI: 10.1145/2976749.2978392
[PDF, BibTeX, talk video, project page, ]
Secure digital home / access control for non-security-experts: This collection of projects explores architectures, mechanisms, and interfaces for helping users manage access control in the digital home of the future and on online social networks. Recent research includes new methods to discover smart-home configurations that may leak information, new ways to specify access-control policies (e.g., reactively, and via metadata-based policy rules), and using machine learning to help users specify security policies and privacy preferences.
Towards usable security analysis tools for trigger-action programming.
McKenna McCall, Eric Zeng, Faysal Hossain Shezan, Mitchell Yang, Lujo Bauer, Abhishek Bichhawat, Camille Cobb, Limin Jia, and Yuan Tian.
In SOUPS '23: Proceedings of the 19th Symposium on Usable Privacy and Security, August 2023. USENIX. © authors
[PDF, BibTeX, talk video and slides, ]
“I would have to evaluate their objections”: Privacy tensions between smart home device owners and incidental users.
Camille Cobb, Sruti Bhagavatula, Kalil Anderson Garrett, Alison Hoffman, Varun Rao, and Lujo Bauer.
Proceedings on Privacy Enhancing Technologies, 2021 (4). October 2021. De Gruyter Open. © authors DOI: 10.2478/popets-2021-0060
[PDF, BibTeX, talk video, ]
How risky are real users' IFTTT applets?
Camille Cobb, Milijana Surbatovich, Anna Kawakami, Mahmood Sharif, Lujo Bauer, Anupam Das, and Limin Jia.
In SOUPS '20: Proceedings of the 16th Symposium on Usable Privacy and Security, August 2020. © authors
[PDF, BibTeX, 5-min talk (+ slides), 14-min talk, ]
Some recipes can do more than spoil your appetite: Analyzing the security and privacy risks of IFTTT recipes.
Milijana Surbatovich, Jassim Aljuraidan, Lujo Bauer, Anupam Das, and Limin Jia.
In Proceedings of the 26th International World Wide Web Conference, April 2017. © IW3C2, CC BY 4.0 DOI: 10.1145/3038912.3052709
[PDF, BibTeX, video from PrivacyCon, ]
(Do not) Track me sometimes: Users' contextual preferences for web tracking.
William Melicher, Mahmood Sharif, Joshua Tan, Lujo Bauer, Mihai Christodorescu, and Pedro Giovanni Leon.
Proceedings on Privacy Enhancing Technologies (2). April 2016. De Gruyter Open. © authors DOI: 10.1515/popets-2016-0009
[PDF, BibTeX, slides, talk video, ]
Sharing personal content online: exploring channel choice and multi-channel behaviors.
Manya Sleeper, William Melicher, Hana Habib, Lujo Bauer, Lorrie Faith Cranor, and Michelle L. Mazurek.
In CHI'16: 34th Annual ACM Conference on Human Factors in Computing Systems, May 2016. ACM. © authors DOI: 10.1145/2858036.2858170
[PDF, BibTeX, video teaser, ]
Toward strong, usable access control for shared distributed data.
Michelle L. Mazurek, Yuan Liang, William Melicher, Manya Sleeper, Lujo Bauer, Gregory R. Ganger, Nitin Gupta, and Michael K. Reiter.
In Proceedings of the 12th USENIX Conference on File and Storage Technologies (FAST '14), February 2014. USENIX.
[PDF, BibTeX, talk video, ]
Challenges faced in working with users to design access-control systems for domestic environments.
Manya Sleeper, Michelle L. Mazurek, and Lujo Bauer.
In Designing with Users for Domestic Environments workshop at CSCW14 (the 17th ACM Conference on Computer Supported Cooperative Work and Social Computing), February 2014. Position paper.
[PDF, BibTeX, ]
The post anachronism: The temporal dimension of Facebook privacy.
Lujo Bauer, Lorrie Faith Cranor, Saranga Komanduri, Michelle L. Mazurek, Michael K. Reiter, Manya Sleeper, and Blase Ur.
In Proceedings of the 12th Annual Workshop on Privacy in the Electronic Society, November 2013. ACM. © authors DOI: 10.1145/2517840.2517859
[PDF, BibTeX, ]
What you want is not what you get: Predicting sharing policies for text-based content on Facebook.
Arunesh Sinha, Yan Li, and Lujo Bauer.
In Proceedings of the 6th ACM Workshop on Security and Artificial Intelligence, November 2013. ACM. © authors DOI: 10.1145/2517312.2517317
[PDF, BibTeX, ]
What matters to users? Factors that affect users' willingness to share information with online advertisers.
Pedro G. Leon, Blase Ur, Yang Wang, Manya Sleeper, Rebecca Balebako, Richard Shay, Lujo Bauer, Mihai Christodorescu, and Lorrie Faith Cranor.
In SOUPS '13: Proceedings of the 9th Symposium on Usable Privacy and Security, July 2013. ACM. © authors DOI: 10.1145/2501604.2501611
[PDF, BibTeX, ]
Out of sight, out of mind: Effects of displaying access-control information near the item it controls.
Kami Vaniea, Lujo Bauer, Lorrie Faith Cranor, and Michael K. Reiter.
In Proceedings of the 2012 Tenth Annual International Conference on Privacy, Security and Trust (PST), pages 128--136, July 2012. IEEE. © IEEE DOI: 10.1109/PST.2012.6297929
[PDF, BibTeX, ]
Tag, you can see it! Using tags for access control in photo sharing.
Peter F. Klemperer, Yuan Liang, Michelle L. Mazurek, Manya Sleeper, Blase Ur, Lujo Bauer, Lorrie Faith Cranor, Nitin Gupta, and Michael K. Reiter.
In CHI 2012: Conference on Human Factors in Computing Systems, pages 377--386, May 2012. ACM. © ACM DOI: 10.1145/2207676.2207728
[PDF, BibTeX, ]
Exploring Reactive Access Control.
Michelle L. Mazurek, Peter F. Klemperer, Richard Shay, Hassan Takabi, Lujo Bauer, and Lorrie Faith Cranor.
In CHI '11: Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, pages 2085--2094, May 2011. ACM. © ACM DOI: 10.1145/1978942.1979245
[PDF, BibTeX, ]
Access control for home data sharing: Attitudes, needs and practices.
Michelle L. Mazurek, J.P. Arsenault, Joanna Breese, Nitin Gupta, Iulia Ion, Christina Johns, Daniel Lee, Yuan Liang, Jenny Olsen, Brandon Salmon, Richard Shay, Kami Vaniea, Lujo Bauer, Lorrie Faith Cranor, Gregory R. Ganger, and Michael K. Reiter.
In CHI 2010: Conference on Human Factors in Computing Systems, pages 645--654, April 2010. ACM. © ACM DOI: 10.1145/1753326.1753421
[PDF, BibTeX, ]
Security and privacy for the Internet of
Things (IoT) outside the home: IoT devices are becoming ubiquitous. They enable
fantastic new functionality, but also present new security
and privacy risks. We try to discover these risks and develop solutions that
address them.
Attributions for ML-based ICS anomaly detection: From theory to practice. Perspectives from a comprehensive evaluation of reconstruction-based anomaly detection in industrial control systems. The influence of friends and experts on privacy decision making in IoT scenarios. Privacy expectations and preferences in an IoT world. Self-driving cars and data collection: Privacy perceptions of networked autonomous vehicles. Towards privacy-aware smart buildings: Capturing, communicating, and enforcing privacy policies and preferences. Publications
Clement Fung, Eric Zeng, and Lujo Bauer.
In Proceedings of the 31st Network and Distributed System Security Symposium, February 2024. Internet Society. © authors DOI: 10.14722/ndss.2024.23216
[PDF, BibTeX, talk video, code, ]
Clement Fung, Shreya Srinarasi, Keane Lucas, Hay Bryan Phee, and Lujo Bauer.
In ESORICS 2022: 27th European Symposium on Research in Computer Security, September 2022. © authors DOI: 10.1007/978-3-031-17143-7_24
[PDF, BibTeX, talk video, code, ]
![]() “Did you know this camera tracks your mood?”: Understanding privacy expectations and preferences in the age of video analytics.
“Did you know this camera tracks your mood?”: Understanding privacy expectations and preferences in the age of video analytics.
Shikun Zhang, Yuanyuan Feng, Lujo Bauer, Lorrie Cranor, Anupam Das, and Norman Sadeh.
Proceedings on Privacy Enhancing Technologies, 2021 (2). April 2021. De Gruyter Open. 2022 Privacy Papers for Policymakers Award. © authors DOI: 10.2478/popets-2021-0028
[PDF, BibTeX, ]
Pardis Emami Naeini, Martin Degeling, Lujo Bauer, Richard Chow, Lorrie Cranor, Mohammad Reza Haghighat, and Heather Patterson.
In Proceedings of the 21st ACM Conference on Computer-Supported Cooperative Work and Social Computing, November 2018. © authors DOI: 10.1145/3274317
[PDF, BibTeX, ]
Pardis Emami-Naeini, Sruti Bhagavatula, Hana Habib, Martin Degeling, Lujo Bauer, Lorrie Cranor, and Norman Sadeh.
In SOUPS '17: Proceedings of the 13th Symposium on Usable Privacy and Security, July 2017. USENIX. © authors
[PDF, BibTeX, slides, audio, ]
Cara Bloom, Joshua Tan, Javed Ramjon, and Lujo Bauer.
In SOUPS '17: Proceedings of the 13th Symposium on Usable Privacy and Security, July 2017. USENIX. © authors
[PDF, BibTeX, slides, audio, ]
Primal Pappachan, Martin Degeling, Roberto Yus, Anupam Das, Sruti Bhagavatula, William Melicher, Pardis Emami Naeini, Shikun Zhang, Lujo Bauer, Alfred Kobsa, Sharad Mehrotra, Norman Sadeh, and Nalini Venkatasubramanian.
In International Workshop on the Internet of Things Computing and Applications, June 2017. In conjunction with ICDCS2017.
[BibTeX, ]
Online tracking: While we browse the web our behavior is observed by online trackers, which construct profiles of users based on the websites we visit. These profiles are used to select ads and show content customized to our interests, but trackers also invade our privacy. We study how much tracking users are subjected to and whether tools like privacy-preserving web browsers and browser extensions like Ghostery can help.
Widespread third-party tracking on hospital websites poses privacy risks for patients and legal liability for hospitals.
Ari B. Friedman, Raina M. Merchant, Amey Maley, Karim Farhat, Kristen Smith, Jackson Felkins, Rachel E. Gonzales, Lujo Bauer, and Matthew S. McCoy.
Health Affairs, 42 (4) 508-515. 2023. DOI: 10.1377/hlthaff.2022.01205
[PDF, BibTeX, ]
Prevalence of third-party tracking on abortion clinic web pages.
Ari B. Friedman, Lujo Bauer, Rachel Gonzales, and Matthew S. McCoy.
JAMA Internal Medicine. 2022. DOI: 10.1001/jamainternmed.2022.4208
[PDF, BibTeX, ]
Investigating advertisers' domain-changing behaviors and their impacts on ad-blocker filter lists.
Su-Chin Lin, Kai-Hsiang Chou, Yen Chen, Hsu-Chun Hsiao, Darion Cassel, Lujo Bauer, and Limin Jia.
In Proceedings of The Web Conference, April 2022. © ACM DOI: 10.1145/3485447.3512218
[PDF, BibTeX, talk video, ]
![]() OmniCrawl: Comprehensive measurement of Web tracking with real desktop and mobile browsers.
OmniCrawl: Comprehensive measurement of Web tracking with real desktop and mobile browsers.
Darion Cassel, Su-Chin Lin, Alessio Buraggina, William Wang, Andrew Zhang, Lujo Bauer, Hsu-Chun Hsiao, Limin Jia, and Timothy Libert.
Proceedings on Privacy Enhancing Technologies, 2022 (1). January 2022. De Gruyter Open. PETS 2022 Artifact Award. © authors DOI: 10.2478/popets-2022-0012
[PDF, BibTeX, code, talk video, slides, ]
(Do not) Track me sometimes: Users' contextual preferences for web tracking.
William Melicher, Mahmood Sharif, Joshua Tan, Lujo Bauer, Mihai Christodorescu, and Pedro Giovanni Leon.
Proceedings on Privacy Enhancing Technologies (2). April 2016. De Gruyter Open. © authors DOI: 10.1515/popets-2016-0009
[PDF, BibTeX, slides, talk video, ]
Passwords: Although they are often insecure and inconvenient, passwords aren't quite about to disappear. This project's goal is to help users create passwords that are easy for them to remember, but hard for attackers to guess. We work towards this goal by trying to deeply understand the password-creation process and the security of the resulting passwords, including by investigating the effects of password-composition policies and password meters on the security and usability of passwords, and by studying metrics for quantifying password strength.
(How) Do people change their passwords after a breach?
Sruti Bhagavatula, Lujo Bauer, and Apu Kapadia.
USENIX ;login:. December 2021. USENIX. © authors
[PDF, BibTeX, ]
Practical recommendations for stronger, more usable passwords combining minimum-strength, minimum-length, and blocklist requirements.
Joshua Tan, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In Proceedings of the 27th ACM SIGSAC Conference on Computer and Communications Security, November 2020. ACM. © authors DOI: 10.1145/3372297.3417882
[PDF, BibTeX, talk video, ]
Why people (don't) use password managers effectively.
Sarah Pearman, Aerin Shikun Zhang, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In SOUPS '19: Proceedings of the 15th Symposium on Usable Privacy and Security, July 2019. © authors
[PDF, BibTeX, ]
User behaviors and attitudes under password expiration policies.
Hana Habib, Pardis Emami-Naeini, Maggie Oates, Chelse Swoopes, Lujo Bauer, Lorrie Faith Cranor, and Nicolas Christin.
In SOUPS '18: Proceedings of the 14th Symposium on Usable Privacy and Security, August 2018. © authors
[PDF, BibTeX, slides, ]
“It's not actually that horrible”: Exploring adoption of two-factor authentication at a university.
Jessica Colnago, Summer Devlin, Maggie Oates, Chelse Swoopes, Lujo Bauer, Lorrie Faith Cranor, and Nicolas Christin.
In CHI'18: 36th Annual ACM Conference on Human Factors in Computing Systems, April 2018. ACM. © authors DOI: 10.1145/3173574.3174030
[PDF, BibTeX, teaser video, ]
Better passwords through science (and neural networks).
William Melicher, Blase Ur, Sean Segreti, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
USENIX ;login:, 42 (4). December 2017. USENIX. © authors
[PDF, BibTeX, official version, ]
Let's go in for a closer look: Observing passwords in their natural habitat.
Sarah Pearman, Jeremy Thomas, Pardis Emami Naeini, Hana Habib, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, Serge Egelman, and Alain Forget.
In Proceedings of the 24th ACM SIGSAC Conference on Computer and Communications Security, October 2017. ACM. © authors DOI: 10.1145/3133956.3133973
[PDF, BibTeX, ]
Diversify to survive: Making passwords stronger with adaptive policies.
Sean Segreti, William Melicher, Saranga Komanduri, Darya Melicher, Richard Shay, Blase Ur, Lujo Bauer, Nicolas Christin, Lorrie Cranor, and Michelle L. Mazurek.
In SOUPS '17: Proceedings of the 13th Symposium on Usable Privacy and Security, July 2017. USENIX. © authors
[PDF, BibTeX, slides, audio, ]
![]() Design and evaluation of a data-driven password meter.
Design and evaluation of a data-driven password meter.
Blase Ur, Felicia Alfieri, Maung Aung, Lujo Bauer, Nicolas Christin, Jessica Colnago, Lorrie Cranor, Harold Dixon, Pardis Emami Naeini, Hana Habib, Noah Johnson, and William Melicher.
In CHI'17: 35th Annual ACM Conference on Human Factors in Computing Systems, May 2017. ACM. CHI Best Paper. © authors DOI: 10.1145/3025453.3026050
[PDF, BibTeX, video teaser, code, online demo, ]
Password creation in the presence of blacklists.
Hana Habib, Jessica Colnago, William Melicher, Blase Ur, Sean Segreti, Lujo Bauer, Nicolas Christin, and Lorrie Cranor.
In Proceedings of Usable Security (USEC) 2017, February 2017. Internet Society. © Internet Society DOI: 10.14722/usec.2017.23043
[PDF, BibTeX, slides, ]
![]() Fast, lean, and accurate: Modeling password guessability using neural networks.
Fast, lean, and accurate: Modeling password guessability using neural networks.
William Melicher, Blase Ur, Sean M. Segreti, Saranga Komanduri, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In Proceedings of the 25th USENIX Security Symposium, August 2016. USENIX Security Best Paper.
[PDF, BibTeX, video teaser, slides, talk video, code, ]
![]() Do Users' Perceptions of Password Security Match Reality?
Do Users' Perceptions of Password Security Match Reality?
Blase Ur, Jonathan Bees, Sean Segreti, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In CHI'16: 34th Annual ACM Conference on Human Factors in Computing Systems, May 2016. ACM. CHI 2016 Honorable Mention. © authors DOI: 10.1145/2858036.2858546
[PDF, BibTeX, video teaser, online game, ]
Measuring Real-World Accuracies and Biases in Modeling Password Guessability.
Blase Ur, Sean M. Segreti, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, Saranga Komanduri, Darya Kurilova, Michelle L. Mazurek, William Melicher, and Richard Shay.
In Proceedings of the 24th USENIX Security Symposium, August 2015. USENIX. © authors
[PDF, BibTeX, talk video, video teaser, ]
The impact of length and mathematical operators on the usability and security of system-assigned one-time PINs.
Patrick Gage Kelley, Saranga Komanduri, Michelle L. Mazurek, Richard Shay, Tim Vidas, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In 2013 Workshop on Usable Security (USEC), volume 7862 of Lecture Notes in Computer Science, pages 34--51, April 2013. Springer. © Springer-Verlag DOI: 10.1007/978-3-642-41320-9_3
[PDF, BibTeX, ]
How does your password measure up? The effect of strength meters on password creation.
Blase Ur, Patrick Gage Kelley, Saranga Komanduri, Joel Lee, Michael Maass, Michelle Mazurek, Timothy Passaro, Richard Shay, Timothy Vidas, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In Proceedings of the 21st USENIX Security Symposium, August 2012. USENIX Association. © authors
[PDF, BibTeX, talk video, ]
Correct horse battery staple: Exploring the usability of system-assigned passphrases.
Richard Shay, Patrick Gage Kelley, Saranga Komanduri, Michelle L. Mazurek, Blase Ur, Tim Vidas, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In SOUPS '12: Proceedings of the 8th Symposium on Usable Privacy and Security, July 2012. ACM. © authors DOI: 10.1145/2335356.2335366
[PDF, BibTeX, ]
![]() Guess again (and again and again): Measuring password strength by simulating password-cracking algorithms.
Guess again (and again and again): Measuring password strength by simulating password-cracking algorithms.
Patrick Gage Kelley, Saranga Komanduri, Michelle L. Mazurek, Richard Shay, Tim Vidas, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, and Julio Lopez.
In Proceedings of the 2012 IEEE Symposium on Security and Privacy, pages 523--537, May 2012. IEEE. IEEE Test of Time award, 2023 © IEEE DOI: 10.1109/SP.2012.38
[PDF, BibTeX, ]
![]() Of passwords and people: Measuring the effect of password-composition policies.
Of passwords and people: Measuring the effect of password-composition policies.
Saranga Komanduri, Richard Shay, Patrick Gage Kelley, Michelle L. Mazurek, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, and Serge Egelman.
In CHI '11: Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, pages 2595--2604, May 2011. ACM. CHI 2011 Honorable Mention. © ACM DOI: 10.1145/1978942.1979321
[PDF, BibTeX, ]
I'm fortunate to advise and work with many talented students, postdocs, and staff, including:
Students and postdocs I advised or worked with closely:
PhD students: Scott Garriss (CMU ECE, PhD 2008; now at Snowflake),
Rob Reeder (CMU CSD, advised by Lorrie Cranor, PhD 2008; now at Google),
Kami Vaniea (CMU CSD, PhD 2012, co-advised with Lorrie Cranor; now at University of Waterloo),
Michelle Mazurek (CMU ECE, co-advised with Greg Ganger, PhD 2014; now at University of Maryland at College Park),
Saranga Komanduri (CMU COS, advised by Lorrie Cranor, PhD 2016),
Keane Lucas (CMU ECE, PhD 2024; now at Anthropic),
Xiaoxiao Tang (visiting PhD student from SMU, Singapore),
Blase Ur (CMU SC, advised by Lorrie Cranor, PhD 2016; now at University of Chicago),
Yannis Mallios (CMU ECE, PhD 2017, now at Google Pittsburgh),
Jassim Aljuraidan (CMU ECE, PhD 2018, now at Kuwait University),
Billy Melicher (CMU ECE, PhD 2019, now at Palo Alto Networks),
Mahmood Sharif (CMU ECE, PhD 2019, now at Tel Aviv University),
Josh Tan (CMU Societal Computing, PhD 2020, now at Amazon),
Sruti Bhagavatula (CMU Societal Computing, PhD 2021, now at Northwestern University),
Trevor Kann,
Keane Lucas (CMU ECE, PhD 2024, now at Anthropic),
Weiran Lin (CMU ECE, PhD 2025, now at Grey Swan),
Andy Gallardo (CMU Societal Computing, PhD 2025),
Clement Fung (CMU ECE, PhD 2025),
Nuno Sabino (CMU-Portugal CS PhD 2025, co-advised with Limin Jia, Pedro Adão, Rui Maranhão), Brian Singer (CMU ECE, PhD 2025, co-advised with Vyas Sekar).
Postdocs:
Omer Akgul (S3D postdoc 2023–2024),
Matthias Beckerle (CyLab postdoc 2014–2015, now at Karlstad University),
Camille Cobb (CyLab postdoc 2019–2021, now at the University of Illinois Urbana-Champaign),
McKenna McCall (S3D postdoc 2023–2025, next position: Assistant Professor, Colorado State University)
Willard Rafnsson (CyLab postdoc 2015–2017, now at the IT University of Copenhagen),
Eric Zeng (CyLab postdoc 2022–2024),
.
Others:
Sean Segreti (CMU ECE, MS 2016; now KoreLogic),
Shaoying Cai (visiting PhD student from SMU, Singapore, 2014),
Tony Felice (CMU ECE ugrad/masters),
Elli Fragkaki (CMU ECE, MS 2013),
Wataru Hasegawa (CMU INI masters),
Philip Seyoung Huh (CMU ECE, MS 2014),
Joel Lee (CMU Heinz masters, 2013),
Sudeep Modi (CMU INI masters),
Sean Segreti (CMU ECE masters, 2015),
Brad Miller (CMU ECE, BS 2009),
Timothy Passaro (CMU ECE, BS/MS 2014),
Ariel Rao (CMU undergraduate),
This material is presented to ensure timely dissemination of scholarly and technical work. Copyright and all rights therein are retained by authors or by other copyright holders. All persons copying this information are expected to adhere to the terms and constraints invoked by each author's copyright. In most cases, these works may not be reposted without the explicit permission of the copyright holder.
new! User perceptions vs. proxy LLM judges: Privacy and helpfulness in LLM responses to privacy-sensitive scenarios.
Xiaoyuan Wu, Roshni Kaushik, Wenkai Li, Lujo Bauer, and Koichi Onoue.
In Proceedings of the 64th Annual Meeting of the Association for Computational Linguistics, July 2026. To appear.
[BibTeX, ]
new! Incalmo: An autonomous LLM-assisted system for red teaming multi-host networks.
Brian Singer, Keane Lucas, Lakshmi Adiga, Meghna Jain, Lujo Bauer, and Vyas Sekar.
In Proceedings of the 47th IEEE Symposium on Security and Privacy, May 2026. To appear.
[BibTeX, ]
new! U.S. Southerners' attitudes towards AI analysis of voice data for high-stakes employment and education evaluations.
Andrea Gallardo, Lily Klucinec, Lujo Bauer, and Lorrie Faith Cranor.
In Proceedings of the 29th ACM Conference on Computer-Supported Cooperative Work and Social Computing, October 2026. To appear.
[BibTeX, ]
new! Passing down passwords: How older adults approach postmortem account access and digital estate planning.
Jenny Tang, Xiaoyuan Wu, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor.
In CHI '26: Proceedings of the 2026 CHI Conference on Human Factors in Computing Systems, April 2026. ACM. © authors DOI: 10.1145/3772318.3791633
[PDF, BibTeX, ]
new! Location-enhanced information flow for home automations.
McKenna McCall, Benjamin Weinshel, Kunlin Cai, Ying Li, Eric Zeng, Devika Manohar, Lujo Bauer, Limin Jia, and Yuan Tian.
Proceedings on Privacy Enhancing Technologies, 2026 (1). 2026. © authors DOI: 10.56553/popets-2026-0018
[PDF, BibTeX, data and code, ]
DOM-XSS detection via webpage interaction fuzzing and URL component synthesis.
Nuno Sabino, Darion Cassel, Rui Abreu, Pedro Adão, Lujo Bauer, and Limin Jia.
In Proceedings of the 33rd Network and Distributed System Security Symposium, February 2026. Internet Society. © authors DOI: 10.14722/ndss.2026.231467
[PDF, BibTeX, code, ]
![]() Estimating LLM consistency: A user baseline vs surrogate metrics.
Estimating LLM consistency: A user baseline vs surrogate metrics.
Xiaoyuan Wu, Weiran Lin, Omer Akgul, and Lujo Bauer.
In Proceedings of the 2025 Conference on Empirical Methods in Natural Language Processing, November 2025. Association for Computational Linguistics. Senior Area Chair Highlight DOI: 10.18653/v1/2025.emnlp-main.1554
[PDF, BibTeX, talk video, data and code, ]
The impact of device type, data practices, and use case scenarios on privacy concerns about eye-tracked augmented reality in the United States and Germany.
Efe Bozkir, Babette Bühler, Xiaoyuan Wu, Enkelejda Kasneci, Lujo Bauer, and Lorrie Faith Cranor.
Journal of Cybersecurity, 11 (1). November 2025. Oxford University Press. © authors DOI: 10.1093/cybsec/tyaf036
[PDF, BibTeX, ]
Perry: A high-level framework for accelerating cyber deception experimentation.
Brian Singer, Yusuf Saquib, Lujo Bauer, and Vyas Sekar.
In Proceedings of the 28th International Symposium on Research in Attacks, Intrusions and Defenses (RAID 2025), October 2025. DOI: 10.1109/RAID67961.2025.00049
[PDF, BibTeX, code, ]
Misuse, misreporting, misinterpretation of statistical methods in usable privacy and security papers.
Jenny Tang, Lujo Bauer, and Nicolas Christin.
In SOUPS '25: Proceedings of the 21st Symposium on Usable Privacy and Security, August 2025. USENIX. © authors
[PDF, BibTeX, slides, video, supplemental data, ]
Adopting AI to protect industrial control systems: Assessing challenges and opportunities from the operators’ perspective.
Clement Fung, Eric Zeng, and Lujo Bauer.
In SOUPS '25: Proceedings of the 21st Symposium on Usable Privacy and Security, August 2025. USENIX. © authors
[PDF, BibTeX, slides, video, ]
“I would still use it but I wouldn't trust it”: Evaluating mechanisms for transparency and control for smart-home sensors.
Benjamin Weinshel, Yuvraj Agarwal, and Lujo Bauer.
Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies, 9 (2). June 2025. ACM. © authors DOI: 10.1145/372948
[PDF, BibTeX, dataset, ]
Updated 2026.04.22.
Copyright © Lujo Bauer